As if fighting outside hack attacks are not enough, IT departments everywhere are combating another foe: company social media websites. These websites and the content employees post to them pose a challenge to keep that information from harming cybersecurity efforts. Most companies have social media sites that post information about the company, including plenty of pictures and comments about social gatherings. Employees are welcome to post business-oriented content, as well as their own pictures and comments. It all sounds innocent enough, but hackers who troll these sites are only interested in what they can glean from them and then use it to hack employees and company data systems. IT departments should be on high alert for their websites and do what they can to prevent TMI (Too Much Information) from being posted.
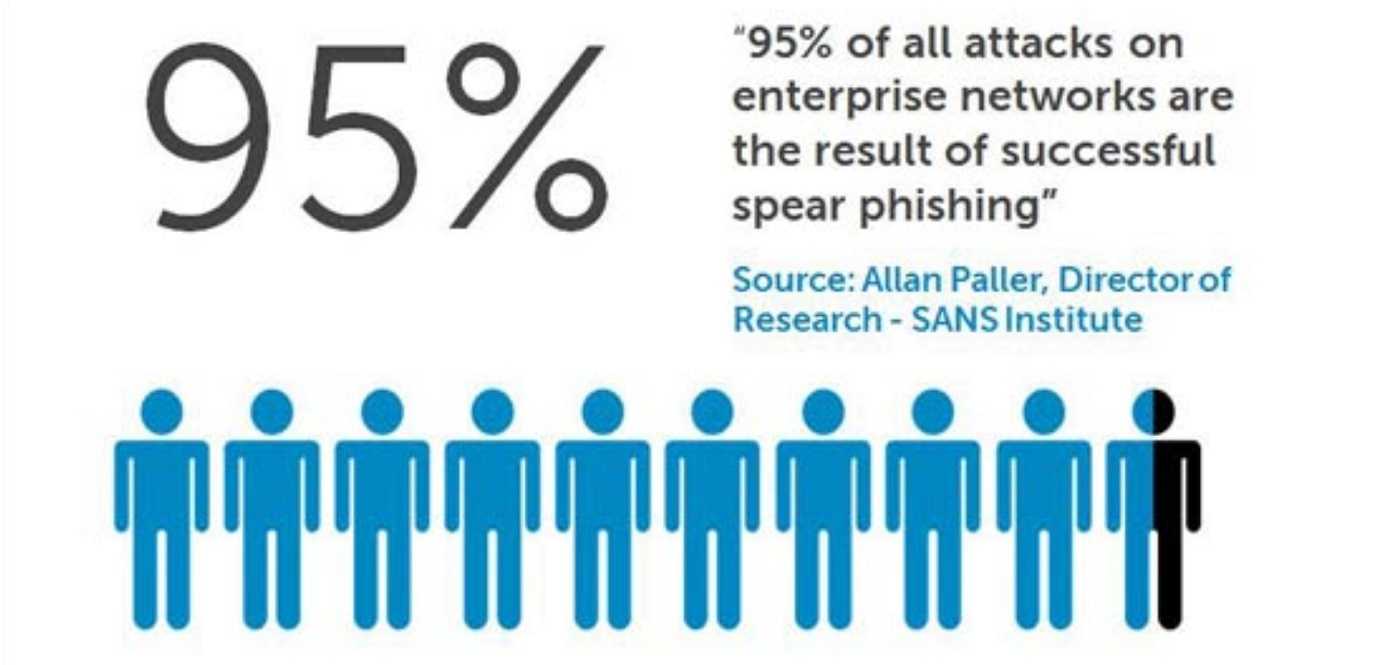
Hackers easily take advantage of TMI to launch email phishing, smishing (texting) and vishing (phone) attacks. The information they get from a company social media website is unusually valuable, allowing them to specifically target employees, known as spearphishing. Hackers use names and any vendor information posted on a company social media website to look like something they are not; legitimate. They try to phish, smish, and vish their way into an organization. Some of their goals are compromising data systems by using malicious attachments and bogus websites. They also make voice calls aimed at getting sensitive information by claiming to be vendors or some other connection to the company. IT personnel have their work cut out for them with all of the outside–and inside–threats to cybersecurity. Proofpoint offers tips to help keep IT departments in the driver’s seat and secure a tight lid on their company social media websites.
 Create strict guidelines. Policies, restrictions, and processes for social media are necessary official guidelines about what should never be posted by employees. Continually review and update guidelines to mitigate risks posed by ever-changing hacking trends and risks.
Create strict guidelines. Policies, restrictions, and processes for social media are necessary official guidelines about what should never be posted by employees. Continually review and update guidelines to mitigate risks posed by ever-changing hacking trends and risks.
- Secure devices. Especially in a BYOD (Bring Your Own Device) environment, all devices need to be secured with updated anti-malware security software. Any and all personal devices used for work need this security and employees should never use a device not approved and secured by IT. Devices should also be able to have content remotely erased should they be lost or stolen.
- Keep everyone in-the-loop. Make sure that any outside vendors and cybersecurity providers are also aware of the company guidelines and policies for social media use. Always keep them informed of any adjustments and changes in policy so they know what to be aware of.
- Limit access to social media. Make sure that only approved vendors and employees have access to accounts. Should an employee or vendor cut ties with the company, immediately delete their access to company websites.
- Educate everyone. Ongoing employee cybersecurity education is a necessary part of keeping themselves and company data systems secure. Hackers never stop–and neither should employee education.
© Copyright 2018 Stickley on Security Inc.
 An official website of the State of North Dakota
An official website of the State of North Dakota